Ensuring email delivery is critical for every business. All the main email providers like Gmail, Outlook and Yahoo employ multi-layered email authentication techniques. Your email email has to pass each one to land in an inbox. Depending on the authentication failure your email may be filtered to Spam/Junk or rejected altogether. You are probably familiar with most of the components of email authentication. Your server must have a reverse DNS entry, your domain must have an SPF record and your mail server IP cannot be blacklist in the popular RBLs. But most people don’t know they should also be authenticating email with DKIM and DMARC.
All our servers have reverse DNS and DNS zones have SPF records by default. We monitor blacklists and work hard to delist IPs very quickly if they appear. Our newer servers add DMARC records by default too. But DKIM is something you need to enable in Plesk.
So What is DKIM?
DKIM (DomainKeys Identified Mail) is an email authenticating system that works differently from the more well-known SPF (Sender Policy Framework). An SPF record is an anti-spoofing mechanism that contains a domain’s mail server IP or hostname. A receiving mail server verifies an email is sent from the correct server by doing a DNS lookup on the sending mail server and validating it against the domain’s SPF record.
DKIM is a mechanism that ensures email integrity as well as sender authentication. When you send an email, DKIM digitally signs the email with a cryptographic signature. This “signing essentially encrypts various fields of an email like – like Subject, To and From. The message body is also hashed. The receiving mail server will do a DNS lookup to find your public key. It uses this to decrypt the encoded values in the email’s header and also (and critically) recalculate the hash value for the mail message in it’s entirety. If these two values match, this cryptographically proves that the mail was digitally signed by the sending domain. It also ensures integrity as a fully signed email cannot be tampered without and leave an intact signature.
Authenticating Email with DKIM And DMARC In Plesk
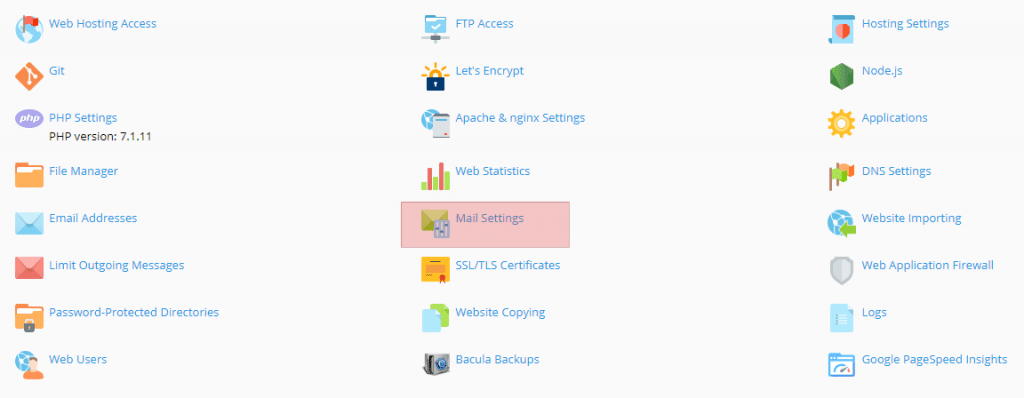
This is super easy. Just navigate to the domain on which you want to enable DKIM and in Websites & Domains you’ll see Mail Settings:
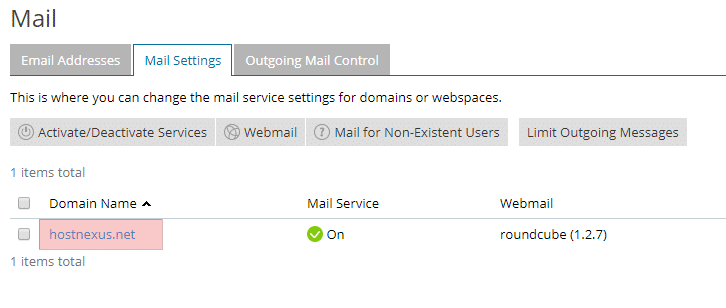
You can also get there by going to Mail > Mail Settings and clicking on your domain name:
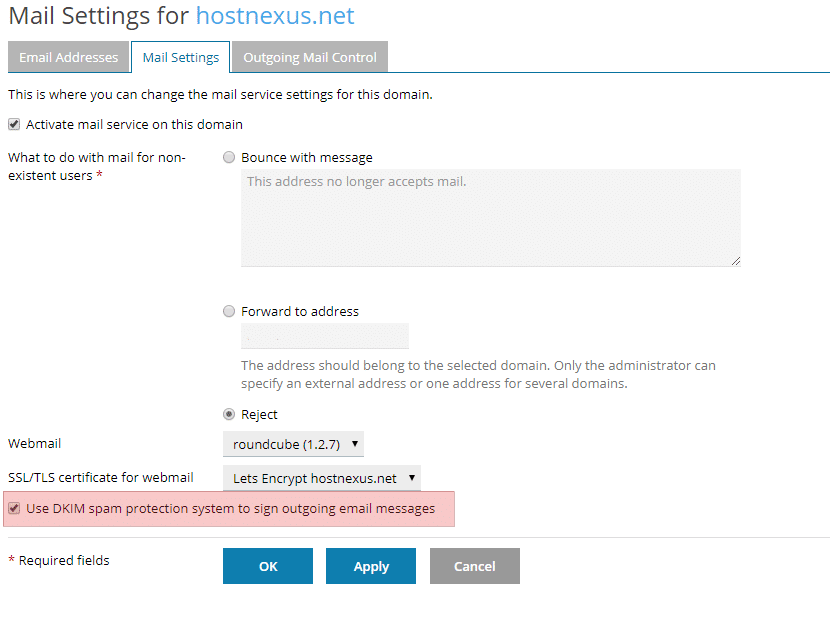
Once there just check the box next to “Use DKIM spam protection system to sign outgoing messages”.
This will also add 2 TXT DNS records to your domain’s DNS Zone:
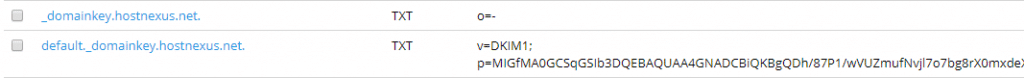
default._domainkey.yourdomain.com– this contains the public part of the generated key._ domainkey.<example.com>– contains the DKIM policy (o=- signifies that all email from the domain is signed with DKIM)
Testing DKIM
You can test that DKIM is working with this online tool. Click Next Step and send an email to the generated email address. You should wait a few hours after activating DKIM to allow for DNS propagaion before you test. DKIM should show a pass and you’ll see the signed section of the header. For example:
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=hostnexus.com; s=default; t=1511688990; bh=DqEtqzPQ2e4o5M2xavMLvRMPu/PUj4NjLSKeo41DAeg=; l=590; h=Received:Subject:From:To; b=l+E/b0imuGRF3Sbd8Ss/kloA14xLniC7rFhG/do8tIB/1rXrgIWV0wQTyWOaie8qg 4tnu6VgH2N2oFZYerk3hxNVkL4KKhIKNKzVg/Aobf2CdeYWEWojDEW4Zslgj2c5A5E QNXddzec6yV3NxRsE1GbroRePcbeOM/D0OvjABug= |
For those that are interested here is a simple explainer on the various components:
- v is the DKIM version.
- a is the signing algorithm. RSA is the public key cryptosystem and SHA256 is the cryptgraphic hash (output).
- c is the canonicalization (data conversion) algorithm.
- d is your domain.
- s is the selector (this is always “default” in Plesk and set in your DNS record).
- t is the signature timestamp.
- bh is the computed body hash.
- l is the length of the canonicalized part of the body that has been signed.
- h is the list of signed header fields.
- b is the actual digital signature.
Enabling DMARC
DMARC (Domain-based Message Authentication) is an authentication method that extends the capabilities of both SPF and DKIM. DMARC helps email receivers determine if the purported message “aligns” with what the receiver knows about the sender. If not, DMARC includes guidance on how to handle the “non-aligned” messages.As I said earlier, our later servers already have this record in its DNS template so all newly created domains will have it. To enable it you simply need to go to your DNS Settings and add a TXT record that says _dmarc with a value of v=DMARC1; p=none.
![]()
The standard user won’t need to go any deeper into DMARC’s capabilities.
Test Your Email With Mail-Tester.com
If you move to a new server or you suspect you are having email delivery problems mail-tester.com is my favorite tool for testing mail configurations. Send an email to the generated email address and click the button.
With correctly configured rDNS (as all our servers have), no blacklisting, SPF, DKIM and DMARC records it shouldn’t be hard to get 10/10.

If you are scoring less than 10/10 please contact our support team and we’ll get you there in no time. Scoring 10/10 is still no guarantee of email deliverability at Gmail, Outlook, Hotmail etc but this is your starting point for sure. When I check my own HN email I was getting 10/10 but I had 2 orange check marks instead of green.
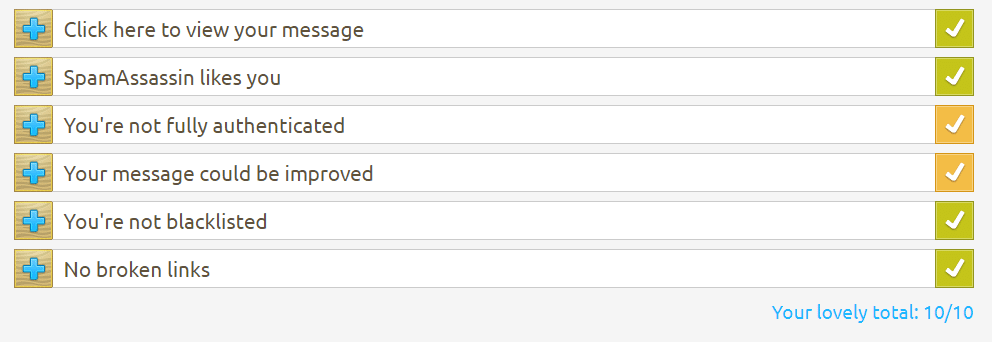
Intrigued by this I dug deeper and found that I was missing the DMARC record.
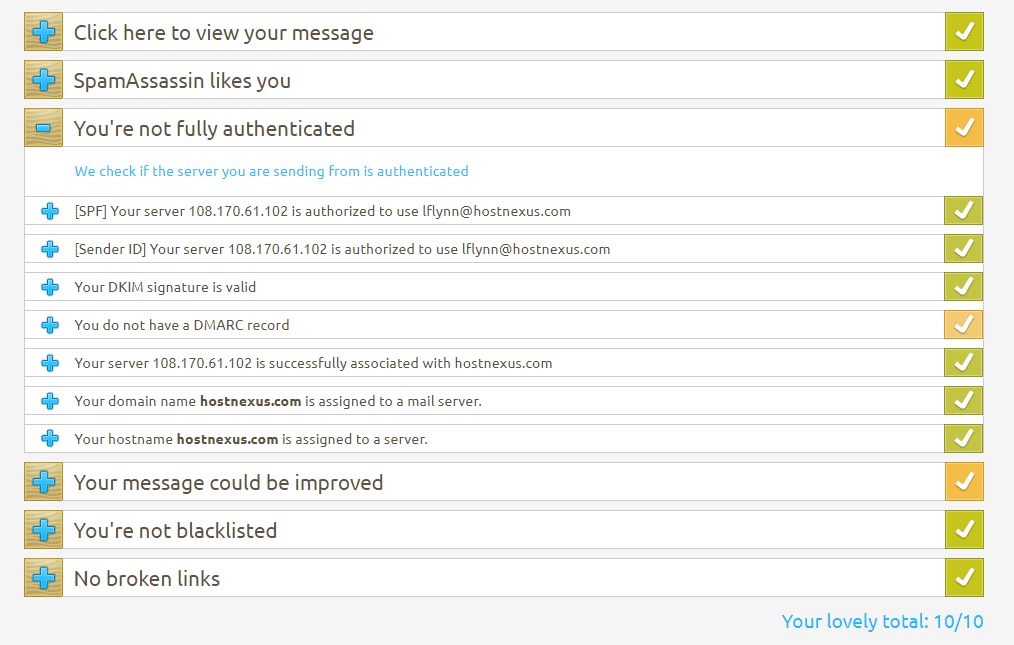
DMARC records shouldn’t affect deliverability but why take the risk? It takes 2 seconds to add a DMARC record and even if the top providers don’t use it as a metric for accepting email now that could always change. The other orange check mark pertains to a “Link Unsubscribe” header field – only needed for mailing lists.





Thanks very much for this, Laurence. What an improvement! I have both yahoo.com and outlook.com web email accounts. Prior to making the change, my emails were going to the spam folder on yahoo and not even showing up at all in outlook. Since I made the mods, email goes into the proper inbox of both accounts just as it should.
Yep, hoping to make this general knowledge here at HN. So often we see tickets asking why mail ends up in spam/junk folders and it’s so easy to fix.